The window to exchange $HAI for Hacken Equity Shares ($HES) is now open > Claim your spot today
Looking Back At LCX Hack From January 2022
By Hacken
The beginning of January 2022 was challenging for the crypto exchange LCX. The hacker stole $7.94m through unauthorized access to its hot wallets. The LCX team provided a rapid response and covered all the losses. On Jan 28, 2022, LCX resumed all deposits and withdrawals, meaning the incident was effectively resolved in 20 days. In months that followed, LCX managed to freeze 60% of the stolen crypto through close cooperation with law enforcement.
From a bigger picture, LCX private key compromise demonstrate that custodians must implement rigorous security standards for reliable cryptocurrency asset managemnet and operations.
What Happened?
Private Key Compromise
On January 8th, 2022, the attacker accessed LCX’s Ethereum hot wallets and transferred $7.94m in cryptocurrency to their address. Personal data was never comrpomised.
The hacker withdrew many coins, such as EnjinCoin (ENJ), Monerium EUR (EURe), Quant (QNT), LCX token (LCX), ChainLink (LINK), SAND (SAND), USD Coin (USDC) tokens. A more detailed breakdown:
- 3,437,783.23 USDC ($3.4m )
- 17,251,192.30 LCX Token ($2.4m)
- 761,236.94 EURe ($864k)
- 162.68 ETH ($502k)
- 101,249.71 SAND Token ($486k)
- 669.00 QNT ($115k)
- 1,847.65 LINK ($48k)
- 4,819.74 ENJ ($11k)
The Reason For Private Key Compromise
The question that interested everyone the most, “How did the hacker got access to hot wallets?” LCX never shared the exact cause. What we know instaed is that the main server infrastructure, data storages, wallet management and vaults stood strong. Based on that, we can specualte that it could’ve been related weak operations security. This incident once again proves the need testing all the possible attack vectors.
Only one hot wallet, among LCX’s many, was compromised. Things could have gotten worse, but the tech team noticed the attack minutes after it started so were able to secure other wallets.
LCX Response
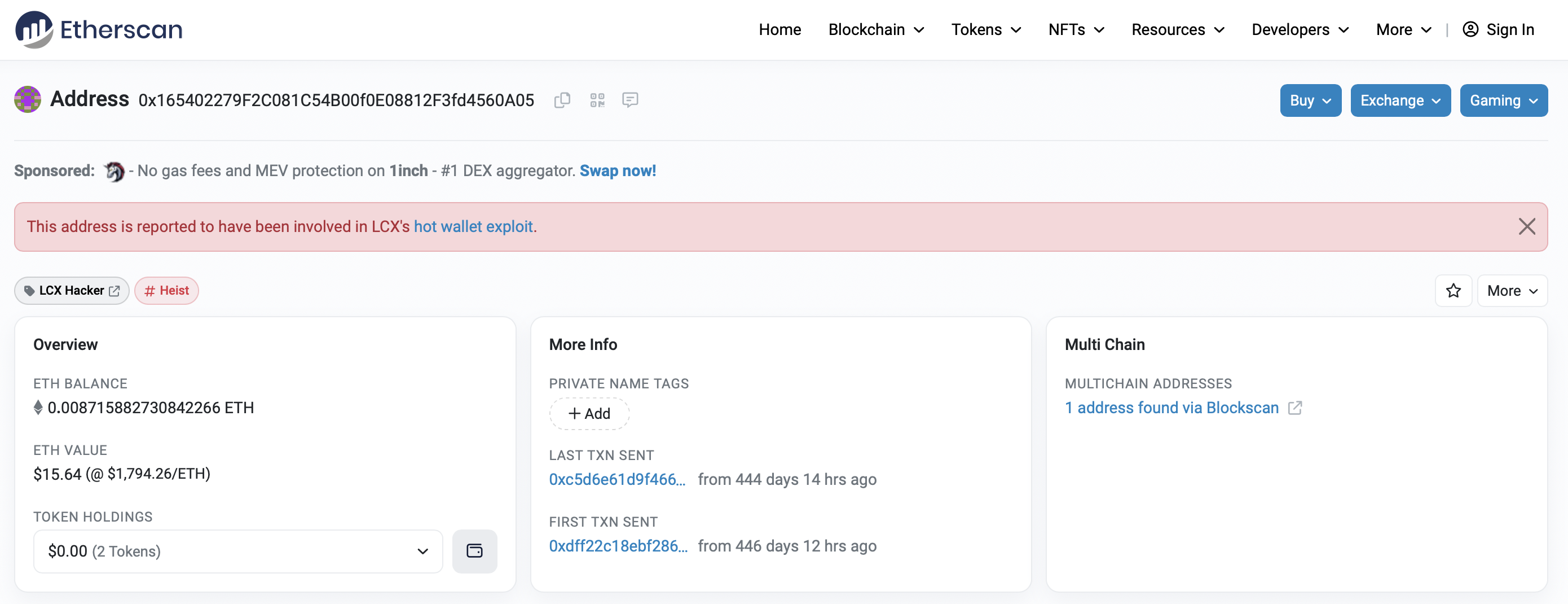
LCX noticed malicious activities within minutes and prevented further damage by taking immediate action. Namely, the deposit and withdrawal functionality of the platform has been put on pause, and LCX notified its partnersabout the security incident. For example, Monerium froze 611,000 EURe and Hacken provided cybersecurity assistance. The company also reported the hacker’s wallet to Etherscan.
LCX specialists completed initial security checks, identified affected assets, and published a detailed incident report. LCX also used its own funds to compensate the affected users. As a result, there was no impact on user balances at LCX.
Catching The Attacker
LCX launched fairly successful investigations with law enforcement in Liechtenstein, Ireland, Spain and USA. They were able to trace stolen funds, even though the attacker uesd Tornado.cash. According to its update on June 22, 2022, 60% of the stolen funds were frozen:
- Lichtenstein court ordered Coinbase to freeze 500 ETH
- New York Supreme Court ordered Centre Consortium to freeze 1.3m USDC
- Serving a temporary restraining order via NFT (first time in history)
This is where being a “regulated trade venue” really made a difference.
Key Elements of Cyber Security Assessments
In 2021, LCX entered into collaboration with the Hacken team. The exchange launched a bug bounty program on HackenProof in September 2021. Between March and October 2021, we concluded a cybersecurity assessment where LCX got a positive security score. The subsequent attack happened three months after the final check.
Our specialists have provided the exchange with a set of recommendations on how to address major security risks. Although hack prevention constitutes a complex process, there is a list of universal recommendations following which crypto exchanges can become resistant to major types of security threats:
Focus on information security policy:
- Maintain security policy covering all personnel and third parties
Secure network perimeter:
- Install and maintain firewalls, web security gateways/data prevention systems
Vulnerability management, penetration testing, and red team exercises:
- Keep antimalware software up to date
- Ensure security across all systems and applications
- Ongoing bug bounty/vulnerability disclosure program
Access control measures:
- Split access to secret data (Two-man rule)
- Limit access to secret data based on business needs
- Limit physical access to secret data
Protecting secret data:
- Encrypting secret data at rest
- Encrypt secret data for transmission
Monitoring:
- Monitor all access to secret data
Insurance:
- Funds Insurance
- The cyber risk or cyber liability insurance
Operation security:
- Periodically reinitialize a hot wallet
- Use secret sharing schemes
- Do not store more than 5% of all deposits in hot wallets
- Store crypto in several hot wallets for each cryptocurrency platform
Following these recommendations is a must-have activity for every reputable crypto exchange. That is why the security of exchange users and their assets heavily depends on the ability of its security team to introduce the appropriate security measures mentioned above.
Recommended Security Framework (CCSS)
In the industry landscape, security standards encompass the key security areas for crypto exchanges. Standards allow projects to comply with regulatory requirements, thereby ensuring that users’ assets are protected.
We strongly recommend projects adopt CryptoCurrency Security Standard (CCSS) for secure key storage and all apsects of cryptocurrecny asset managment and operations. Hacken has 9 (the highest on the market) CCSS Auditors who are certified to perfrom all the necessary procedures of CCSS Audit, which is designed to complement ISO:27001 and SOC2.
SOC 2 and ISO 27001 standards complement each other by giving a project a strategy for protecting its information landscape and demonstrating the environment’s security. SOC 2 and ISO 27001 are the fundamental standards for crypto exchanges. Below is some basic information regarding the importance of these standards for industry players, including exchanges.
Similarities. SOC 2 and ISO 27001 are designed to instill trust in clients that a project is protecting their data. They both cover important dimensions of securing information, including confidentiality, integrity, and availability.
A mapping of their criteria can be found on the AICPA Website, demonstrating ~80% overlap. Projects use these standards to demonstrate to their clients that they are correctly managing information security.
Differences. ISO 27001 key areas are the development and maintenance of an ISMS (information security management system), constituting an overarching method of managing data protection practices.
To become compliant, a project needs to perform a risk assessment, determine and implement security controls, and conduct their review regularly.
Unlike ISO 27001, the key characteristic of SOC 2 is flexibility. It covers 5 Trust Services Principles: Security, Availability, Processing Integrity, Confidentiality and Privacy, but only the first principle is mandatory.
Conclusion
It has been more than a year after the privat key compromise, and the regulating tranding venue is still up and running. LCX has adequately responded to the incident. Their quick, open, and detailed communication helped to clarify what happened and prevented additional damage and panic among their clients, users, and partners. The incident reveals weak points but also points the market in the direction of better adoption of rigorous security standards.


Subscribe to our newsletter
Enter your email address to subscribe to Hacken Reseach and receive notifications of new posts by email.