CCSS Audit

CCSS: the gold standard for cryptocurrency security

Cryptocurrency Security Standard (CCSS) is the industry-recognized benchmark for securing businesses that handle digital assets. Achieving CCSS compliance demonstrates your commitment to protecting customer funds and data.
Protect your assets
Significantly reduce the risk of theft, fraud, and data breaches.
Build unwavering trust
Show customers and partners you prioritize security above all else.
Gain a competitive edge
Stand out in a crowded market by demonstrating a commitment to the highest security standards.
Simplify compliance
Streamline regulatory compliance with a recognized security framework.
Future-proof your business
Stay ahead of evolving threats and regulations.
Cryptocurrency exchanges
Custodial wallet providers
DeFi platforms
NFT marketplaces
Token issuers
And any business that prioritizes the security of its digital assets.


Volodymyr Nosov
Founder and CEO of WhiteBITKey areas covered by CCSS
A comprehensive CCSS audit examines all critical aspects of your security infrastructure, including:
Key Management
Securely generating, storing, handling, using, and recovering cryptographic keys, including detailed incident response plans for key compromise.
Access Controls
Restricting access to sensitive systems and data to authorized personnel only.
Network Security
Implementing strong defenses against cyberattacks and unauthorized access.
Data Protection
Protecting data with encryption, secure backups, and a disaster recovery plan.
Operational Security
Establishing robust security policies, procedures, and employee training.
Logging, Monitoring, and Detection
Continuously monitoring systems for suspicious activity and implementing mechanisms for rapid threat detection and response.
Third-Party Security Testing
Conducting regular penetration testing, vulnerability assessments, and code reviews through independent security experts.
Risk Management Framework
Utilizing a comprehensive framework, aligned with standards like ISO 27001 or NIST.
Compliance and Auditing
Ensuring ongoing adherence to CCSS requirements and continuous security monitoring.
Achieve and maintain CCSS compliance with our comprehensive audit process, designed to guide you through every stage of the audit:
Readiness Assessment and Gap Analysis
We assess your current security controls and architecture against CCSS requirements, identifying gaps and providing a clear roadmap to compliance.
Remediation Guidance and Implementation
Strengthen your security systems with expert guidance and support, including:
Follow-up Review and Certification
A final audit confirms your CCSS compliance, and you'll receive ongoing support to achieve and maintain this critical certification, ensuring your long-term security posture.
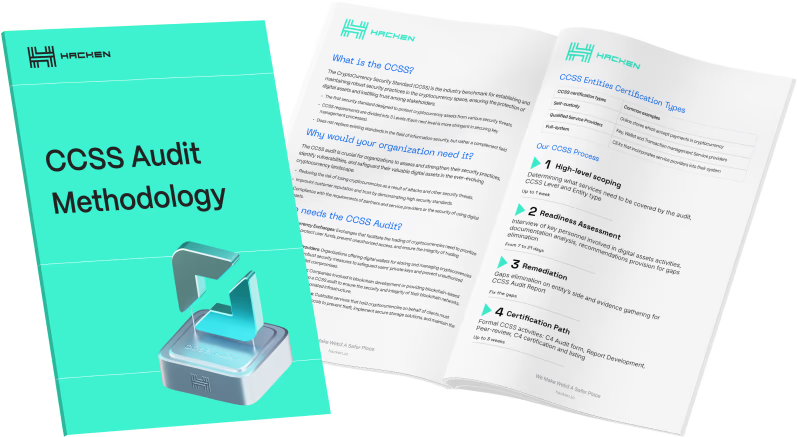
Hacken's proven methodology delivers a thorough and efficient assessment, giving you the confidence that your security controls are up to standard.
Explore our methodologyNavigating the Challenges of CCSS 9.0
CCSS 9.0 introduces more stringent requirements that can be challenging for organizations to implement. Hacken's expertise helps you overcome these hurdles and achieve compliance.
Join 1500+ companies that trust Hacken with their crypto security
Explore our public auditsWeb3 expertise
Entities must assess third-party service providers for compliance with security requirements.
Full compliance support
From initial readiness assessments to achieving full CCSS certification and maintaining ongoing compliance.
ISO 27001 certified
We adhere to the highest international standards for information security management, ensuring the protection of your sensitive data.