Solana Smart Contract Audit
Secure your Solana program before launch or upgrade with a professional security audit designed to identify critical risks, support safe releases, and confirm fixes before production. Built for finance, trading, payments, and protocol teams on Solana.
Security partner for Web3 builders, enterprises, and governments since 2017

- 4114
- critical-to-medium vulnerabilities prevented
- 60+
- certified security engineers
- ISO 27001
- certified
- SOC 2
- type II compliant
Why Solana projects need professional audits
Solana’s account model, CPI patterns, and runtime constraints introduce risk classes that don’t map cleanly to EVM-style audits. A Solana audit needs reviewers who are fluent in Rust patterns and Solana-specific threat models.
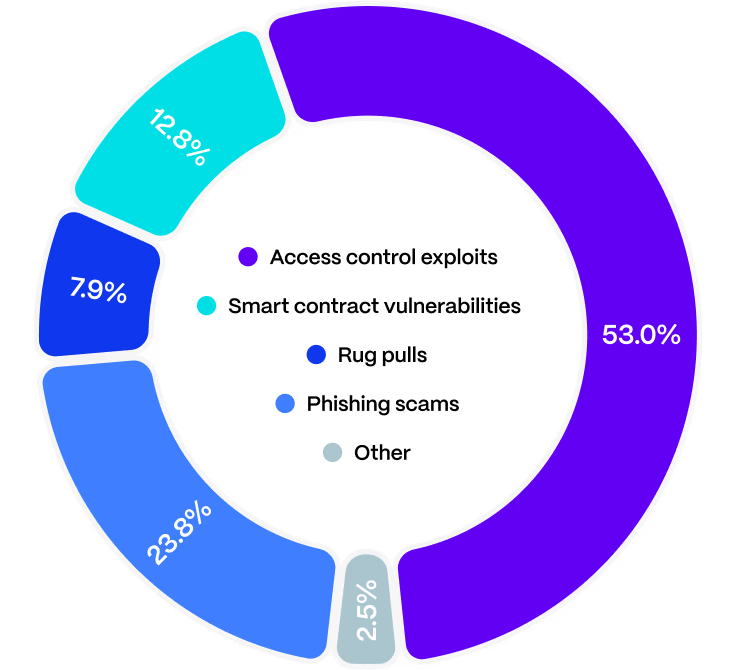
2025 reality check
$4.0B was lost. $512.0M (12.8%) came from smart contract vulnerabilities, while $2.12B (53%) came from access-control failures.
Translation:
code still causes massive losses – but the biggest damage comes from broken authorization and key/control paths. That’s why our Solana audit focuses heavily on who can do what, under which constraints, and how funds move.
Critical Solana vulnerabilities we audit for (and why this matters)
Untrusted accounts & authority checks
We validate owner + signer requirements and critical account relationships so attackers can’t swap in look-alike “config/vault/user” accounts to take control.
Type cosplay & broken invariants
We confirm the right account type, expected addresses, and SPL account properties – especially where “bytes that deserialize” can become “funds that leave”.
CPI safety
We harden CPI call paths by verifying program IDs and constraining accounts – so your program can’t be tricked into authorizing attacker-controlled logic.
Math, precision & accounting edge cases
We test overflow/underflow, truncation, and rounding issues that can silently break balances, fees, or collateral logic.
Token authority & Token-2022 extension risks
We verify mint/burn/freeze/delegate controls, SPL account validation, and extension behaviors that can introduce unexpected privilege or transfer paths.
Upgrades, admin controls & migrations
We analyze upgrade paths, pausability, accounts model changes, and migration safety – code changes introduce a critical risk once real user funds are live.
What you get from a Hacken Solana smart contract audit
Prioritized findings your engineers can ship against
Clear severity, impact, and fix guidance – structured for fast triage and remediation.
Verifiable PoCs for High/Critical issues
For severe findings, we include exploit descriptions as verifiable scenarios so your team (and stakeholders) can understand real-world risk.
A report you can share with partners and exchanges
A clean audit narrative: scope, system overview, risks, findings, definitions, fuzz/invariant results if applied.
Remediation verification
You can submit in-scope remediations within two weeks; we re-check fixes, confirm they don't introduce new risks, and update statuses for the final report.
Real-time visibility in Hacken Portal
Track progress, collaborate with the team, and manage findings in one place with role-based involvement and live tracking.

Our Solana audit reports
Verifiable reports trusted by exchanges and partners:
Explicit scope, audited commits, changelog, and verified remediation steps.
"We work closely with you to define the scope, timeline, and budget that meet your specific needs and expectations. Then, we prepare the testing environment and unit tests to ensure an optimal process and maximum value."
Hacken's Solana audit process
A repeatable methodology built for speed and depth: double manual coverage, structured testing, and real-time reporting – followed by QA and verified remediation.
Explore our audit methodologyHear from our clients
FAQ
Ready to discuss your Solana audit scope?
Share your repo, scope, and timeline – we'll propose an audit plan and estimate.