According to the Crystal blockchain report, $400M were stolen from centralized exchanges and $1,8B from DeFi services in 2021.
The largest hack in 2021 was the Bitmart incident when attackers stole $200M in various cryptocurrencies. The stolen virtual assets were withdrawn from the exchange’s hot wallet. The hack became possible due to the private key leakage.
New Metrics
At the end of 2021, CER included ISO 27001 and Exchange Funds Insurance in our methodology. Without these metrics, an exchange cannot get the maximum score.
ISO 27001 is a fundamental standard for crypto exchanges to follow. It covers important dimensions of securing information including confidentiality, integrity, and availability. ISO 27001 key areas are the development and maintenance of an ISMS (information security management system), which constitutes an overarching method of managing data protection practices.
To become compliant a project needs to perform a risk assessment, determine and implement security controls, and conduct their review regularly. The accredited bodies perform the audit of crypto exchanges to determine whether they are ISO 27001 compliant. For example, in 2019, one of the biggest crypto exchanges Binance was examined on 114 criteria across 14 categories. ISO compliant exchanges apply a structured approach to managing sensitive data and assets. ISO 27001 also covers internal control over private keys. Thus, if Bitmart had followed ISO 27001, very likely, it would not have suffered from the private key leakage.
The CER team also recommends crypto exchanges to become SOC 2 compliant. SOC 2 is a voluntary security standard developed by the American Institute of CPAs. The key characteristic of SOC 2 is flexibility. It covers 5 Trust Services Principles: Security, Availability, Processing Integrity, Confidentiality and Privacy, but only the first principle is mandatory. Both ISO 27001 and SOC 2 are globally recognized, but if you operate in North America, it is strongly recommended to be SOC 2 compliant. SOC 2 attestation is conducted by a licensed certified public accountant. SOC 2 compliance proves that an exchange has an effective process in place to monitor unusual system activity, authorized and unauthorized changes in system configurations, and access control. SOC 2 also focuses on whether an exchange has security alerting practices in place to immediately react to a security incident. SOC 2 compliance ensures the long-term efficiency of the exchange's internal security practices.
2021 Results
In the current analysis, CER has reviewed 301 crypto exchanges.
The primary goal of this report is to provide an expert view of the state of cybersecurity in the crypto exchanges industry.
In November 2021, we updated the score: now there are letters instead of figures, it resembles traditional ratings such as S&P.
Statistics
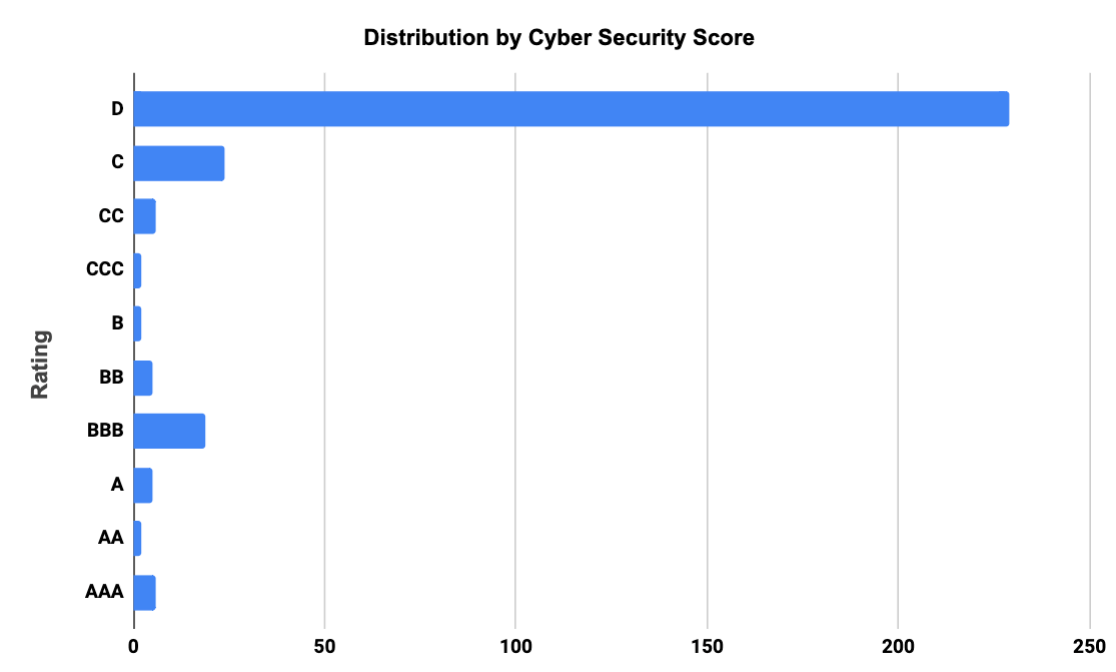
| Rating | Number of Exchanges |
| AAA | 6 |
| AA | 2 |
| A | 5 |
| BBB | 19 |
| BB | 5 |
| B | 2 |
| CCC | 2 |
| CC | 6 |
| C | 24 |
| D | 230 |
Table 1. Scoring stats
The New CSS results show that 32 crypto exchanges (10.66%) out of 301 have received a “good” cybersecurity score (BBB and higher, see Table 1). X2 increase vs. 2021!
During 2021, we received >100 certification requests. Ratings have changed significantly based on the revelations of our latest research.
Compared to the previous top 100 research, the number of exchanges running bug bounty programs has increased from 77 to 98 (+27%). Under the Cer.live methodology, the weight of self-hosted bug bounty programs is two times smaller than those managed by independent third-party platforms with large communities of ethical hackers. Only independent platforms can ensure the fairness of the program and guarantee that the hacker will be rewarded for every identified vulnerability.
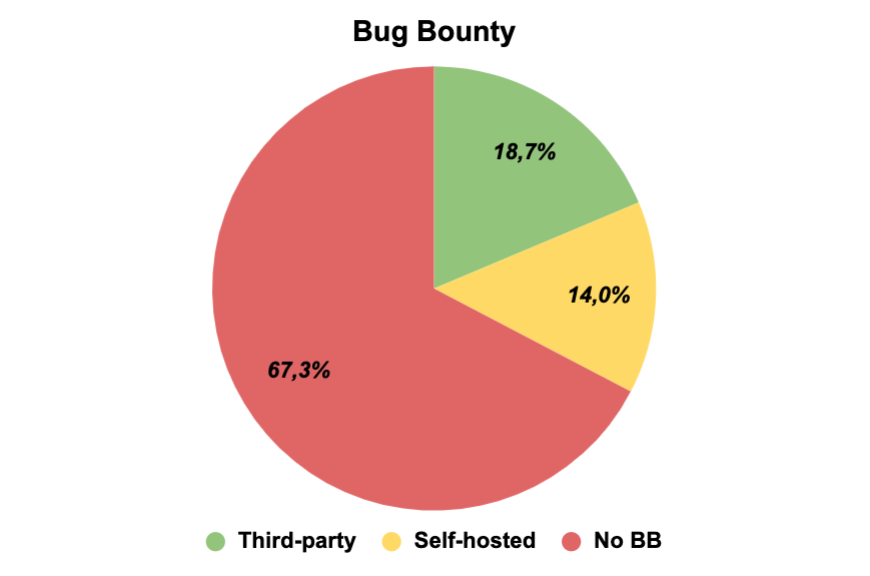
The share of bug bounty programs managed by third-party platforms has increased by 50% since the beginning of 2021. The majority of bug bounty programs are hosted on the following platforms:
- HackenProof
- HackerOne
- Slowmist
- BugCrowd
According to our data, 51 (17% from all) exchanges regularly apply for pentests conducted by different cybersecurity firms.
Thus, the crypto exchanges market becomes more mature year by year.
6 crypto exchanges have the highest rating AAA. They have almost all required cyber security components in place according to Cer.live methodology.
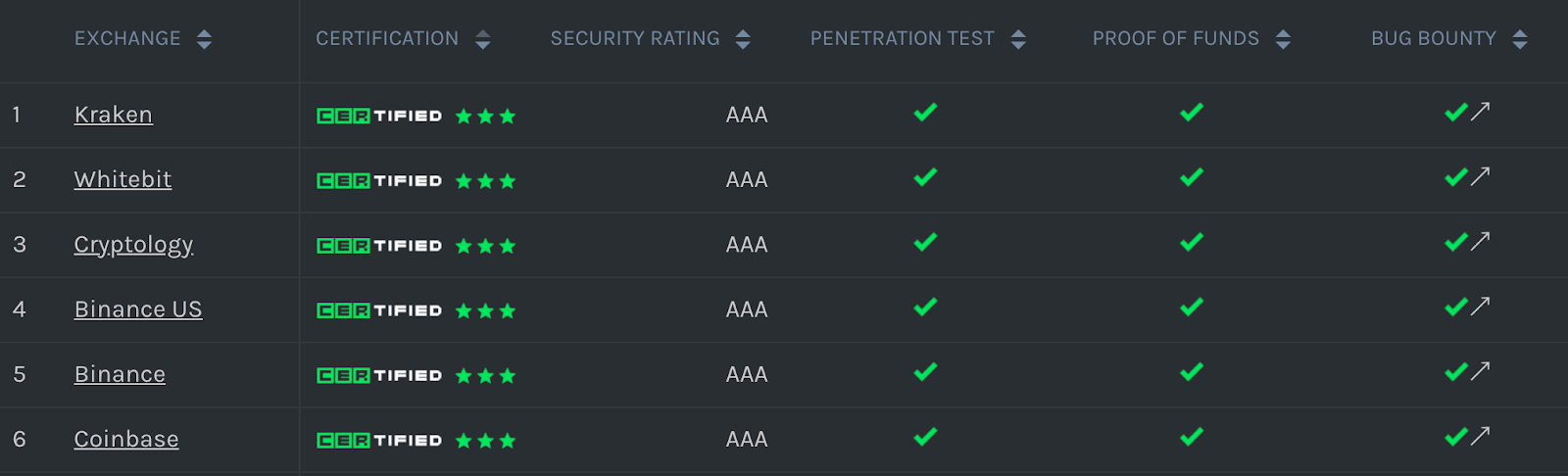
New Top-100 Exchanges by CSS
Below is the table with the cybersecurity rating (both in letters and figures) of each exchange calculated by CER according to the updated methodology.
| # | Exchange | Cybersecurity rating | Rating in figures |
| 1 | CRYPTOLOGY | AAA | 10,00 |
| 2 | KRAKEN | AAA | 10,00 |
| 3 | WHITEBIT | AAA | 10,00 |
| 4 | BINANCE_US | AAA | 9,75 |
| 5 | BINANCE | AAA | 9,55 |
| 6 | COINBASE | AAA | 9,51 |
| 7 | GEMINI | AA | 9,49 |
| 8 | CRYPTO | AA | 9,35 |
| 9 | COINFLEX | A | 9,00 |
| 10 | BLOCKCHAIN | A | 8,98 |
| 11 | HUOBI | A | 8,88 |
| 12 | BITSO | A | 8,53 |
| 13 | BITTREX | A | 8,53 |
| 14 | BYBIT | BBB | 8,49 |
| 15 | CURRENCY | BBB | 8,44 |
| 16 | BITMAX | BBB | 8,43 |
| 17 | BIGONE | BBB | 8,41 |
| 18 | P2PB2B | BBB | 8,33 |
| 19 | WOO | BBB | 8,27 |
| 20 | GATE | BBB | 8,25 |
| 21 | LATOKEN | BBB | 8,20 |
| 22 | FTX_SPOT | BBB | 8,18 |
| 23 | BITMART | BBB | 8,15 |
| 24 | BIKI | BBB | 8,13 |
| 25 | LBANK | BBB | 8,11 |
| 26 | BTSE | BBB | 8,06 |
| 27 | BITRUE | BBB | 8,03 |
| 28 | BITKUB | BBB | 8,03 |
| 29 | BITFINEX | BBB | 8,03 |
| 30 | KUCOIN | BBB | 8,02 |
| 31 | ZB | BBB | 8,02 |
| 32 | HOTBIT | BBB | 8,01 |
| 33 | OKEX | BB | 7,86 |
| 34 | COINMETRO | BB | 7,77 |
| 35 | COINEX | BB | 7,76 |
| 36 | REMITANO | BB | 7,74 |
| 37 | COINSBIT | BB | 7,57 |
| 38 | LCX | B | 7,30 |
| 39 | NICEHASH | B | 7,14 |
| 40 | BITFOREX | CCC | 6,59 |
| 41 | POLONIEX | CCC | 6,53 |
| 42 | CEX | CC | 6,45 |
| 43 | ALTERDICE | CC | 6,43 |
| 44 | B2BX | CC | 6,41 |
| 45 | HOO | CC | 6,37 |
| 46 | AAX | CC | 6,37 |
| 47 | BITCOIN_COM | CC | 6,18 |
| 48 | BITHUMB_GLOBAL | C | 5,86 |
| 49 | INDODAX | C | 5,79 |
| 50 | NARKASA | C | 5,70 |
| 51 | BITOPRO | C | 5,69 |
| 52 | FTX_US | C | 5,68 |
| 53 | STEX | C | 5,65 |
| 54 | BITSTAMP | C | 5,63 |
| 55 | MXC | C | 5,61 |
| 56 | BTCTURK | C | 5,61 |
| 57 | BHEX | C | 5,59 |
| 58 | MAX_MAICOIN | C | 5,54 |
| 59 | TOKENIZE | C | 5,46 |
| 60 | EXMO | C | 5,45 |
| 61 | BKEX | C | 5,42 |
| 62 | ZBG | C | 5,42 |
| 63 | STORMGAIN | C | 5,41 |
| 64 | OTCBTC | C | 5,39 |
| 65 | BITMEX | C | 5,34 |
| 66 | BITBANK | C | 5,31 |
| 67 | BIBOX | C | 5,27 |
| 68 | KUNA | C | 5,25 |
| 69 | XT | C | 5,13 |
| 70 | BITGET | C | 5,03 |
| 71 | DIGIFINEX | C | 5,01 |
| 72 | COINBENE | D | 4,98 |
| 73 | COINSUPER | D | 4,86 |
| 74 | BILAXY | D | 4,50 |
| 75 | BITBNS | D | 4,41 |
| 76 | BW | D | 4,32 |
| 77 | ALTILLY | D | 4,28 |
| 78 | BIT_Z | D | 4,22 |
| 79 | OCEANEX | D | 4,20 |
| 80 | DRAGONEX | D | 4,17 |
| 81 | QTRADE | D | 4,10 |
| 82 | HITBTC | D | 4,08 |
| 83 | TOKENS_NET | D | 4,06 |
| 84 | QUOINE | D | 3,96 |
| 85 | DEXTRADE | D | 3,93 |
| 86 | OKEX_KOREA | D | 3,88 |
| 87 | BTCSQUARE | D | 3,84 |
| 88 | ETOROX | D | 3,84 |
| 89 | BITPANDA | D | 3,82 |
| 90 | FELIXO | D | 3,81 |
| 91 | BANKERA | D | 3,78 |
| 92 | BTCMARKETS | D | 3,78 |
| 93 | OKCOIN | D | 3,70 |
| 94 | FATBTC | D | 3,69 |
| 95 | ZEBPAY | D | 3,65 |
| 96 | DELTA_EXCHANGE | D | 3,64 |
| 97 | ETERBASE | D | 3,59 |
| 98 | EQONEX | D | 3,48 |
| 99 | COINJAR | D | 3,43 |
| 100 | COINHE | D | 3,40 |
Conclusion
Research results show that crypto exchanges are paying greater attention to security since their security level increases every year.
More than 10% of all reviewed exchanges have a good security level. However, there are still issues mostly related to private key management. At least 3 exchanges were hacked due to private key leakage. Exchanges have to perform ISO 27001 and SOC 2 audits to prevent hacks.
We are going to release a big crypto tokens rating in February 2022. Stay updated!
About CER.live
CER.live is a cybersecurity ranking and certification platform that performs security assessments of digital asset platforms based on 18+ indicators. The platform has already evaluated the security of 300+ leading crypto exchanges. Since 2020, the platform has been a trusted partner of CoinGecko and the data provided by CER.live is a part of CoinGecko’s trust score given to exchanges.



