How Hacken A3 detected early signals across bridge activity, Aave borrowing, protocol pauses, and price depeg
TL;DR: During one of 2026’s largest DeFi hacks, Hacken A3 detected the Kelp DAO incident from the first anomalous rsETH release. For asset managers with Aave exposure, that meant earlier visibility to assess risk, reduce exposure, and respond before Aave’s first defensive action and before the broader market fully understood what was happening.
On April 18, 2026, at 17:35 UTC, a risk window opened for every fund, lending desk, and treasury manager with rsETH exposure on Aave.
Most of them didn’t know it yet, but one of the largest DeFi hacks of 2026 was unfolding in real-time. The attacker linked to North Korea’s Lazarus Group had just stolen 116,500 rsETH from KelpDAO’s bridge, worth approximately $292 million, and were about to use Aave lending markets to borrow against the stolen collateral.
At T+0, a fresh address funded through Tornado Cash had received 116,500 rsETH from KelpDAO’s bridge. Minutes later, the exploiter began supplying rsETH to Aave, borrowing WETH at maximum leverage, and expanding exposure across Ethereum and Arbitrum.
At 18:52 UTC, approximately 77 minutes after the first anomalous transfer, Aave executed its first defensive action: freezing rsETH markets.
This did not freeze user funds. But it was a clear protocol-level response to a rapidly developing risk event.
The key question for asset managers was not whether they could prevent the Kelp DAO hack. They could not. The question was whether they had the monitoring signals early enough to assess their Aave exposure and act before risk conditions deteriorated.
That answer depended entirely on what they knew, and when.
Multiple A3 customers had received early signals to assess exposure and reduce or exit positions before Aave risk conditions became obvious to the broader market.
The 77-minute risk assessment window
Here is what was happening on-chain while most funds were unaware.
17:35 UTC. A fresh wallet (funded through Tornado Cash, no legitimate transaction history) received 116,500 rsETH in a single bridge transfer. This was the first signal. Easy to miss if no one is watching.
17:38 UTC. The attacker tested Aave with a 1 rsETH supply. Then, within six minutes: 5,000 rsETH, 20,000, then 27,999 — each immediately followed by a maximum WETH borrow at a loan-to-value ratio of 98.9%. Health factors sitting at 1.01 to 1.03. At this scale, that is not normal market activity. It is someone extracting maximum value as fast as possible.
~18:00 UTC. six other addresses opened rsETH-collateralized positions across Aave v3 on Ethereum and Arbitrum simultaneously. This shows a coordinated operation. The systemic risk was expanding by the minute.
18:18 UTC. Kelp's team paused five core contracts including the OFT Adapter, LRT Deposit Pool, and rsETH token. This was the moment the broader market started paying attention. For most fund managers, this was also the first signal they received. By this point, 43 minutes had already passed.
~18:25 UTC. rsETH/ETH began deviating sharply from the oracle rate on Curve, Uniswap V3, and Uniswap V4. The depeg was now visible to anyone watching DEX prices.
18:52 UTC. Aave froze rsETH markets as its first defensive action.
This was not the moment user funds became frozen. But it was the moment Aave formally restricted rsETH market activity in response to the incident.
What A3 customers knew, and when
A3 is Hacken's continuous on-chain monitoring product. It was running for multiple customers during the Kelp incident. The detection signals.
T+0. A3’s Attack Detector fired on the first highly suspicious interaction: a fresh EOA, funded through Tornado Cash, receiving 116,500 rsETH from the rsETH OFT Adapter in a single lzReceive call. This was the earliest actionable signal.
T+3. High-value borrow and utilization spike on the escalating rsETH supplies and maximum-LTV WETH borrows as they hit the chain.
T+25. Expanding exposure as six other addresses opened rsETH-collateralized positions across Aave V3 on Ethereum and Arbitrum.
T+43. A3 detected Kelp’s protocol pause operations when Kelp’s multisig paused core contracts, including the rsETH OFT Adapter, LRT Deposit Pool, Withdrawal contract, LRT Oracle, and rsETH token.
T+50. sETH/ETH deviation as the depeg developed across Curve, Uniswap V3, and Uniswap V4.
T+77. Aave froze rsETH markets. This was not a freeze of user funds, but it marked the first major defensive action by the lending protocol, which was also flagged by A3 monitoring systems.
For most market participants, the first visible signal may have been Kelp’s protocol pause or the later price deviation. For A3 customers, the first signal came from the initial anomalous rsETH release.
What this means for your risk program
The Kelp hack will not be the last incident of this kind. Liquid restaking tokens, cross-chain bridges, and high-LTV lending positions are a permanent feature of the DeFi landscape — and so are the attackers who know how to exploit them.
Asset managers utilizing Hacken’s A3 have the advantage of earlier visibility: suspicious transfers, high-value borrows, utilization spikes, protocol pauses, and price deviations appearing in one monitoring flow before the broader market fully understood the risk.
What A3 monitors for your portfolio
A3 watches the on-chain activity that matters for funds with DeFi exposure:
- Suspicious interactions: anomalous transfers, Tornado Cash-linked addresses, fresh wallets receiving large amounts.
- High-value borrows and utilization spikes: abnormal LTV ratios, health factors approaching liquidation at scale.
- Protocol pauses and governance actions: multisig executions, emergency freezes, contract pauses across your counterparties.
- Price deviations: secondary market divergence from oracle rates on major DEXs.
- Bridge activity: large cross-chain transfers involving assets in your portfolio.
See it live
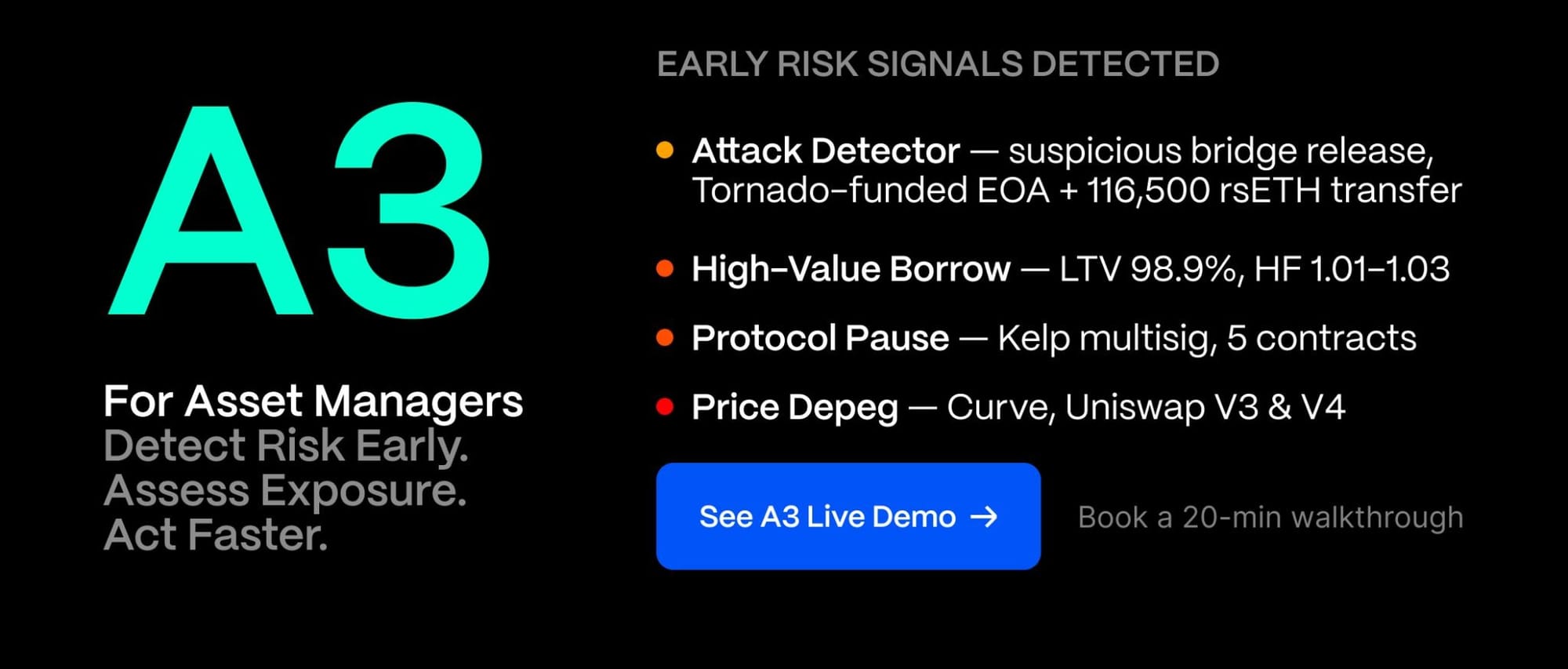
We run short A3 demos using real incidents, including Kelp, as the scenario. In 20 minutes, you’ll see how the alerts would have appeared for your specific assets and counterparties, and how A3 can support faster risk assessment during live DeFi incidents.
Book a demo with João → Calendly